Practical Guide for the Whole Process of Enterprise Trade Secret Protection: Recognition Standards, Protective Measures, and Rights Protection Paths
1、 Identification of trade secrets
Legal concepts and constituent elements:
Article 9 of the revised Anti Unfair Competition Law of China in 2025 defines trade secrets as technical information, business information, and other commercial information that is not known to the public, has commercial value, and has been subject to corresponding confidentiality measures by the rights holder. From this definition, it can also be seen that the three constituent elements of trade secrets are commonly referred to as "secrecy (not widely known and easily accessible to relevant personnel in the field)", "value (able to bring real or potential business benefits)", and "confidentiality (taking reasonable confidentiality measures)".
Business and technical information:
According to Article 1 of the "Provisions of the Supreme People's Court on Several Issues Concerning the Application of Law in the Trial of Civil Cases of Infringement of Trade Secrets" (Interpretation [2020] No. 7), the people's court may determine that information related to technology, such as structure, raw materials, components, formulas, materials, samples, styles, plant new variety propagation materials, processes, methods or their steps, algorithms, data, computer programs and related documents, constitutes technical information as referred to in the Anti Unfair Competition Law. The people's court may determine that the creative, management, sales, financial, planning, sample, bidding materials, customer information, data and other information related to business activities constitute business information as referred to in the Anti Unfair Competition Law. In previous precedents, customer lists, lesson plans, real estate development information, project management operation information, etc. have all been regarded as business information and subsequently recognized as trade secrets by the court.
Judicial recognition standards for trade secrets:
In judicial practice, the determination of secrecy is difficult and usually requires evidence such as appraisal opinions, search reports, or expert opinions to assist in the determination. The rights holder needs to clarify the secret points claimed and bear the preliminary burden of proof in the lawsuit, and then the burden of proof can be transferred to the suspected infringer. The identification process is divided into several stages, including defining confidential points, conducting three character reviews, identifying infringement behavior, and determining identity.
2、 The formulation and implementation of measures to protect trade secrets
The core goal of protecting enterprise trade secrets is not simply to prevent leakage, but to achieve full lifecycle management - from the initial identification of confidential information, to daily protection and dynamic monitoring, to emergency response and rights protection and recovery after leakage, forming a complete management chain; At the same time, the protection of enterprise trade secrets should cover the entire scenario of internal operations (such as research and development, sales, and personnel) and external cooperation (such as suppliers, joint research and development, and customers) to avoid protection loopholes caused by negligence in a certain link.
(1) Organizational and institutional foundations
1. Trade secret management organization:
Enterprises should assign specific personnel and organizations to be responsible for the management of trade secrets. Trade secret management agencies may include:
Trade secret decision-making department: responsible for approving trade secret policies, systems, policies, emergency response to major leakage incidents, and allocating resources required for trade secret management.
→ Trade Secret Management Department: Responsible for formulating trade secret policies, systems, and policies, handling general leakage incidents, coordinating and managing the work responsibilities of various departments in trade secret management, handling specific work such as trade secret employee management, dispute resolution, training and education.
The trade secret responsible persons of each business department are responsible for the implementation of the department's trade secret policies, systems, and policies, and assist the trade secret management department in handling specific tasks such as employee management, dispute resolution, training and education according to the coordination and execution of work responsibilities of the trade secret management department.
2. Improve the system and agreement framework
The core system here is to develop the company's own "Management Measures for Trade Secrets" (clarifying identification standards, grading rules, and confidentiality measures) and "Emergency Response Plan for Leakage Events". In addition, companies also need corresponding supporting documents, such as standardized "Employee Confidentiality Agreement", "Non Competition Agreement", "Visitor Management System", and "Regulations on the Management of Confidential Areas".
(2) Classification and Grading of Trade Secrets
Enterprises should determine corresponding protection measures based on the confidentiality level of trade secrets. The purpose of the classification system for trade secrets is to enable enterprises to prioritize the protection of high-level trade secrets with limited resources, and appropriately reduce the cost of protecting low-level information, thereby improving the overall efficiency of trade secret protection. Overall, it includes three aspects:
1. Establish identification standard process:
Focus on two types of core information, one is technical information: research and development data, process parameters, source code, product design drawings, undisclosed technical achievements, etc; Another type is business and customer information: customer lists (including trading habits, exclusive needs), bidding plans, pricing strategies, cost accounting data, supply chain planning, etc. Each department shall submit new classified information on a monthly (quarterly, semi annual, annual) basis, which shall be reviewed by the Confidentiality Office in conjunction with technical or business experts, and finally entered into the internal "List of Trade Secrets" of the enterprise.
2. Pay attention to the matching of personnel and confidentiality levels:
Enterprises should establish a matching management model for trade secrets and personnel positions based on business models, research and development models, external cooperation models, etc. There are generally two matching modes: one is to match personnel confidentiality levels with access to confidential information based on job level, department, and the degree of exposure required for work; The second is to manage the confidentiality level of personnel in contact with project information based on the importance of confidential information involved in specific projects.
3. Implement a dynamic adjustment mechanism:
Quarterly review of the confidentiality and value of confidential information. If the information is made public (such as patent applications or product launches) or its value decreases, it should be promptly downgraded or decrypted.
(3) Full cycle confidentiality management of staff
Enterprise employees are both users of trade secrets and direct subjects of trade secret leaks. If the system design can enable enterprise employees to manage their trade secrets from the beginning of their employment, it will effectively prevent the leakage of trade secrets from the source. It is crucial to establish a sound employee confidentiality management system, which can be divided into the following three aspects:
1. Entry stage
Background check: Focus on verifying the former employer's confidentiality agreement/non compete agreement performance of core position candidates (such as R&D leader, sales director).
Agreement signing: On the day of employment, employees are required to sign a Confidentiality Agreement, and core positions are required to sign an additional Non Competition Agreement, clearly stating the commitment not to use the former employer's trade secrets.
→ Onboarding training: Explain the company's confidentiality system and the scope of confidential information, distribute the "Employee Confidentiality Handbook" and sign it for confirmation.
2. In service stage
The principle of minimum permission: Assign access permissions to confidential information according to the principle of "necessary for the position" (such as R&D personnel can only access the project code and revoke permissions immediately after the project is completed or employees are transferred).
→ Behavior monitoring: Deploy a data leakage prevention (DLP) system to monitor employees' high-frequency downloads and abnormal behaviors such as cross device transmission; Access control and monitoring are installed in classified areas such as research and development laboratories and server rooms. Visitors must be accompanied by a designated person and registered for record keeping.
Regular audit: Check the employee permission list and confidential file operation logs every six months, identify risks such as "unauthorized access" and "abnormal copying", and promptly identify potential risks.
3. Resignation stage
Resignation review: 15 days before resignation, check the confidential files in the employee's equipment (computer, USB drive), backup and delete key data, and if necessary, notarize the equipment handover process.
→ Data return: Employees are required to return all physical carriers (such as paper drawings and samples), delete confidential information from personal devices, and sign the "Confidentiality Commitment Letter for Resignation".
Non competition tracking: For employees who have signed a non competition agreement, their new employer will be checked monthly. If they violate the agreement, a warning letter will be promptly sent and evidence will be fixed.
(4) Protection of carriers and IT equipment
Trade secrets exist on electronic carriers (computers, servers, cloud drives) or physical carriers (paper documents, USB drives, samples), which are the physical channels for leakage and require targeted protection, mainly divided into the following three aspects:
1. Protection of electronic carriers:
→ Encrypted storage: AES-256 encryption (the most secure symmetric encryption standard today) shall be adopted for core business secret files. Firewall and WAF (Web application firewall) shall be deployed for secret servers, and direct connection to the Internet is prohibited.
→ Access control: Classified files are named and marked with "confidentiality level" (such as the XX algorithm document of "Core Business Secret"), and can only be accessed through internal encrypted cloud drives within the enterprise. Transmission through external tools such as WeChat and email is prohibited.
Backup strategy: Core data is backed up on local servers and encrypted in remote cloud storage. The backup media is encrypted and stored, and the recovery function is tested regularly (monthly) (RTO ≤ 4 hours, RPO ≤ 1 hour).
2. Protection of physical carriers:
Centralized management: Paper confidential documents are stored in locked filing cabinets and kept by dedicated personnel. Borrowing requires approval and registration, and borrowers are required to return them within a limited time.
→ Destruction standard: Waste classified carriers (such as old drawings, USB drives) must be crushed or demagnetized, and destruction records (time, handler, method) must be kept.
3. IT infrastructure security:
Terminal protection: All office computers are equipped with antivirus software and host security protection tools, personal USB drives are disabled, and only enterprise encrypted USB drives are allowed to be used.
Network isolation: Confidential networks are physically isolated from office networks, and remote work requires authentication through a zero trust access system (such as multi factor authentication MFA).
(5) Confidentiality control of external cooperation
When enterprises cooperate with suppliers, service providers, and joint research and development institutions, it is inevitable that they need to provide some information to the other party (such as providing product parameters for suppliers and technical data for joint research and development parties). If not handled properly, there may be intentional or unintentional leakage of information to the outside world during this process. This can be avoided from three aspects:
1. Risk review before cooperation
→ Due diligence: Evaluate the confidentiality capabilities of partners (such as suppliers, service providers, and joint research and development institutions) (such as whether there are sound confidentiality systems and historical leak records).
→ Information desensitization: Sort out the information that needs to be provided to the cooperating party and desensitize the core trade secrets (such as hiding key parameters and simplifying process steps).
2. Agreements and monitoring in cooperation
→ Sign the "Business Cooperation Confidentiality Agreement": clarify the scope of confidentiality (such as technical data and customer information obtained during cooperation), confidentiality period, and breach of contract liability (such as compensation for direct losses and rights protection costs).
→ Cooperation process monitoring: Confidential documents provided to partners are marked as "for cooperative use only" and are prohibited from being lent to third parties; Regularly verify the information usage of partners (such as whether it is used for scenarios beyond the agreement).
3. Data collection after cooperation
Within the specified period after the termination of cooperation, the cooperating party is required to return all confidential carriers (such as technical documents and samples), delete electronic backups, and issue an "Information Destruction Confirmation Letter".
3、 Rights protection strategies when discovering infringement of trade secrets
If a company discovers that a third party is suspected of infringement, it should immediately take investigation and evidence collection measures to preserve the evidence of infringement, and seek legal protection measures, such as sending warning letters, administrative complaints, civil infringement lawsuits, etc. In serious cases, it can also choose to file a criminal report. At the same time, in order to avoid the infringer's vigilance and difficulty in obtaining evidence, before initiating a claim for infringement, it should complete the preliminary investigation and evidence fixation work as much as possible. For example, if an internal employee is suspected of infringing on trade secrets:
If there is already monitoring software deployed internally, the relevant operations and data flow of the employee should continue to be monitored, and a timely decision should be made whether to issue a warning, suspend the employee for investigation, or directly dismiss the employee.
Consider confiscating or sealing the employee's computer or portable hard drive equipment, and notarizing and preserving the handover and sealing process of the equipment (if feasible).
Mirror and copy the data in the sealed equipment, and it is recommended to notarize and preserve the mirroring process (if feasible).
Perform data analysis on the mirrored copy to prevent any improper operation, deletion, or interference with the storage method and content of the original data.
Enterprises should obtain evidence from network resources, product testing information, user manuals, etc. In cases where evidence cannot be obtained from such sources, such as software copyright infringement, detailed source code analysis and reverse engineering techniques should be conducted to collect evidence.
(1) Send a warning letter
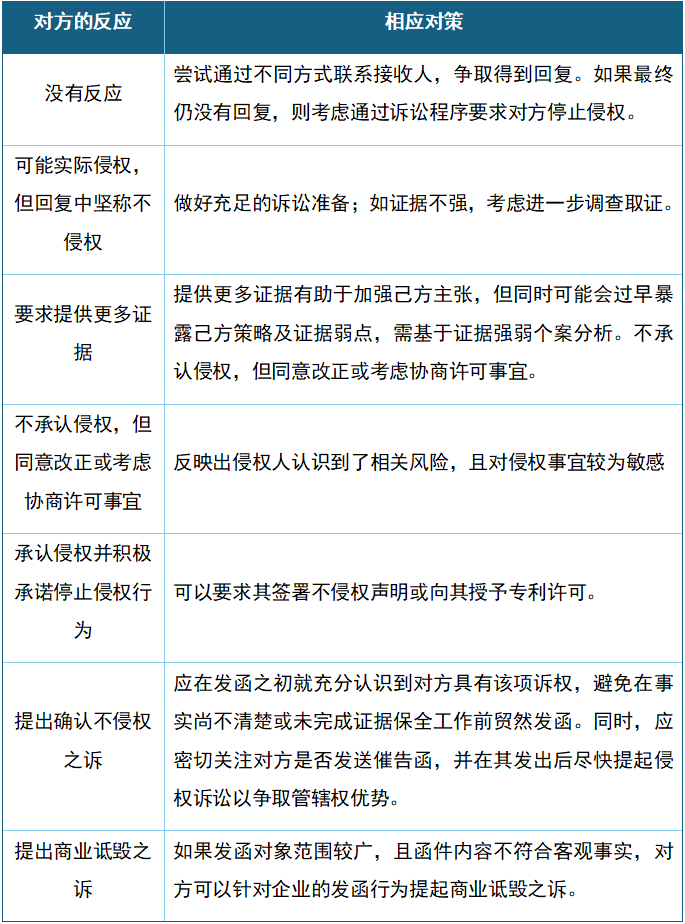
Sending warning letters is one of the most commonly used means in intellectual property rights protection. Before sending a warning letter, it should be ensured that key evidence of infringement has been preserved and necessary litigation or response preparations have been made; After sending a warning letter, different strategic arrangements can be made based on the other party's different reactions.
(2) Initiate civil litigation
If the infringing party receives a warning letter but fails to stop infringing, the enterprise may file a civil lawsuit with the Chinese court with jurisdiction; Enterprises can also choose not to send warning letters and file infringement lawsuits directly. When filing a lawsuit, it is necessary to submit a complaint, a list of evidence, and evidence.
In cases of trade secret infringement, sufficient evidence needs to be submitted to prove that: (1) the information involved constitutes a trade secret (not known to the public, has taken confidentiality measures, has value/practicality) and the carrier of the trade secret; (2) The defendant has the possibility of accessing the company's trade secrets; And (3) the information obtained, disclosed, used, or allowed to be used by the defendant is substantially similar to the technical information claiming the secret point.
Before filing a lawsuit and during the court proceedings, enterprises may apply to the court for behavior preservation, requiring the infringer to immediately cease the infringing behavior. If the court takes action preservation measures, they usually continue until the case judgment takes effect. However, the requirements for behavior preservation applications are relatively high, and the court rarely approves them. In addition, enterprises can also apply to the court for property preservation and evidence preservation to prevent the infringing party from transferring, concealing property or destroying evidence in advance. The relief measures obtained through civil litigation mainly include cessation of infringement (injunction) and compensation for damages.
In recent years, Chinese courts have gradually begun to apply punitive damages mechanisms for malicious infringement of intellectual property rights (including trade secrets). Depending on the severity of the infringement, courts may impose compensation amounts of one to five times the amount in practice to serve as a punishment and warning to infringers.
(3) Initiate administrative litigation
In addition to civil litigation, enterprises can also choose to file administrative complaints with the market supervision and management department of the place where the infringer is located or where the infringement occurred. If the supervisory and management department determines that the infringement of trade secrets is established, it may order the cessation of illegal activities, confiscate illegal gains, and impose fines. However, due to the great difficulty in adjudicating cases of trade secret infringement, the conditions for administrative agencies to file and accept cases are relatively high. Generally, under the premise of meeting the infringement conditions, the range of administrative fines varies from 100000 yuan to 5 million yuan. Moreover, the intervention of public power often has a deterrent effect on infringers during the investigation stage, thereby protecting the trade secrets of rights holders.
(4) File a criminal report
For disputes over trade secret infringement, companies can also choose criminal remedies. In addition to having a complete evidence chain, they also need to meet the filing standards for significant losses. At present, Article 219 of China's Criminal Law stipulates the crime of infringing on trade secrets: "Those who engage in the aforementioned acts of obtaining, disclosing, or using trade secrets, if the circumstances are serious, shall be sentenced to fixed-term imprisonment of not more than three years or detention, and shall also be fined; if the circumstances are particularly serious, they shall be sentenced to fixed-term imprisonment of not less than three years but not more than ten years, and shall be fined." The "serious circumstances" in the Criminal Law usually refers to causing significant losses to the rights holder or having other serious circumstances, and the recognition of "significant losses" is currently limited to 300000 yuan in China's Criminal Law. Serious circumstances belong to open-ended expressions, and in practice, judgments can be made based on factors such as the amount of profits gained by the infringer from illegal operations, the degree to which the right holder's market share has decreased due to infringement, the protection of trade secrets involved, and research and development costs. Enterprises can adopt a combination of criminal, civil, and practical measures to protect trade secrets.
4、 Conclusion
The protection of enterprise trade secrets is not a one-time task, but a systematic engineering that needs to be dynamically optimized based on business development, technological iteration, and external environmental changes. From the improvement of organizational systems, to the daily control of personnel, to the technical protection of carriers and the protection of rights after infringement, each link needs to be closely connected. Only by integrating the awareness of confidentiality into every corner of enterprise operations and effectively protecting all aspects of enterprise activities, including "before, during, and after", can we truly build a secure defense line for trade secrets and safeguard the core competitiveness of the enterprise.
Related recommendations
- Are Microsoft Software Restricted under U.S. Export Controls?
- Interpretation of the Measures for the Administration of the Collection and Use of Personal Information in Internet Applications (Draft for Comments) —— Strengthened Supervision on Personal Information Collection
- One Article to Understand the Compliance Key Points of the Employer of Record (EOR) Model
- Rogue Drone Flights Are a Criminal Offense—Compliant Flying Is No Casual Matter